The multitrillion-dollar car industry has in recent years become a common target for cybersecurity attacks. No company is immune—not Kia, and not Ferrari. Now, cybersecurity researchers have warned of a potential new avenue of attack: Unsecured production lines, which could put customers in danger.
The risk was called to attention by Nozomi Networks Labs, which found vulnerabilities in a Bosch Rexroth smart pneumatic torque wrench that it says is used on car production lines. Its smart functions allow it to send activity data to a central server for logging, as well as receive remote reprogramming for different torque settings.

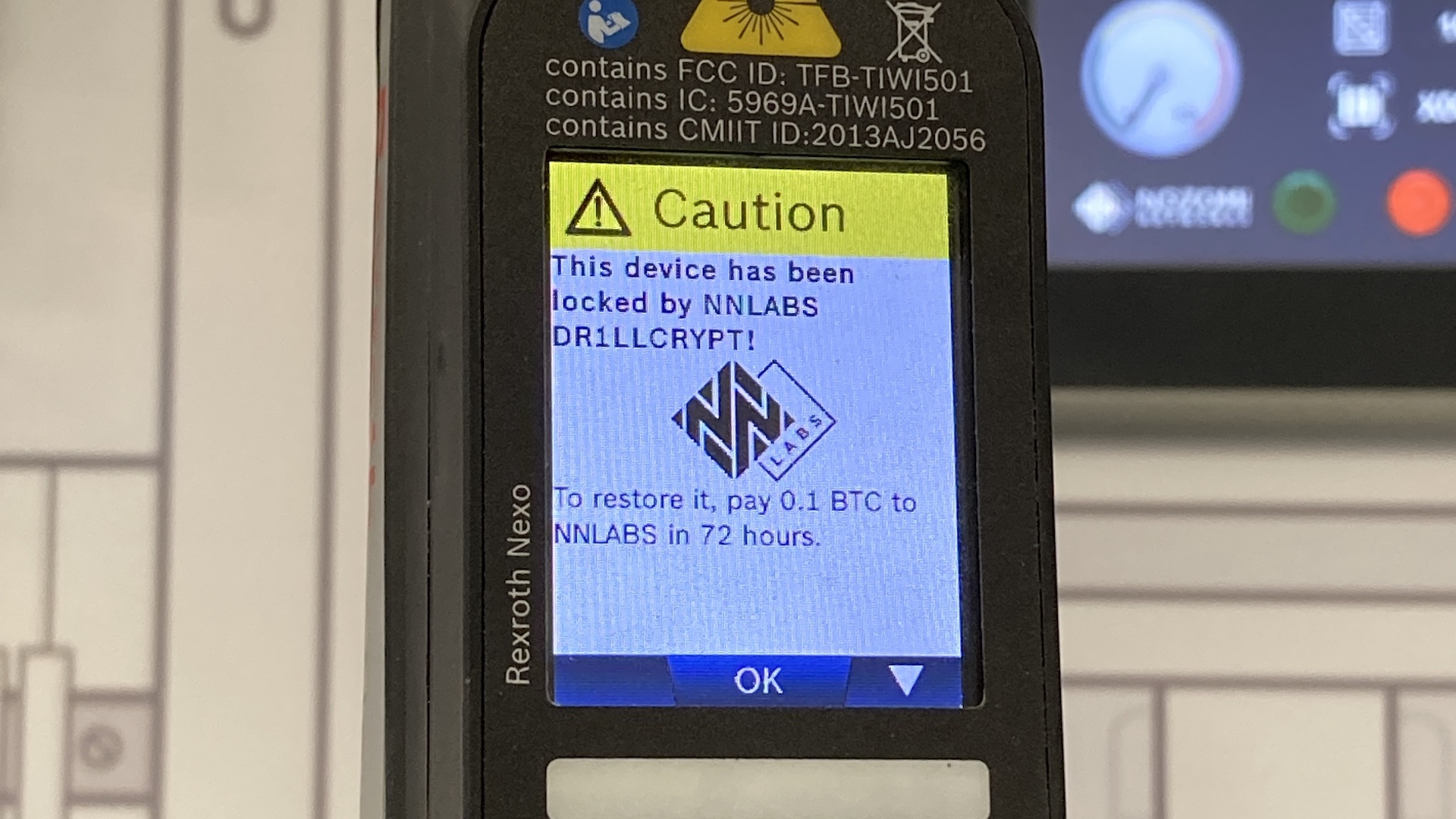
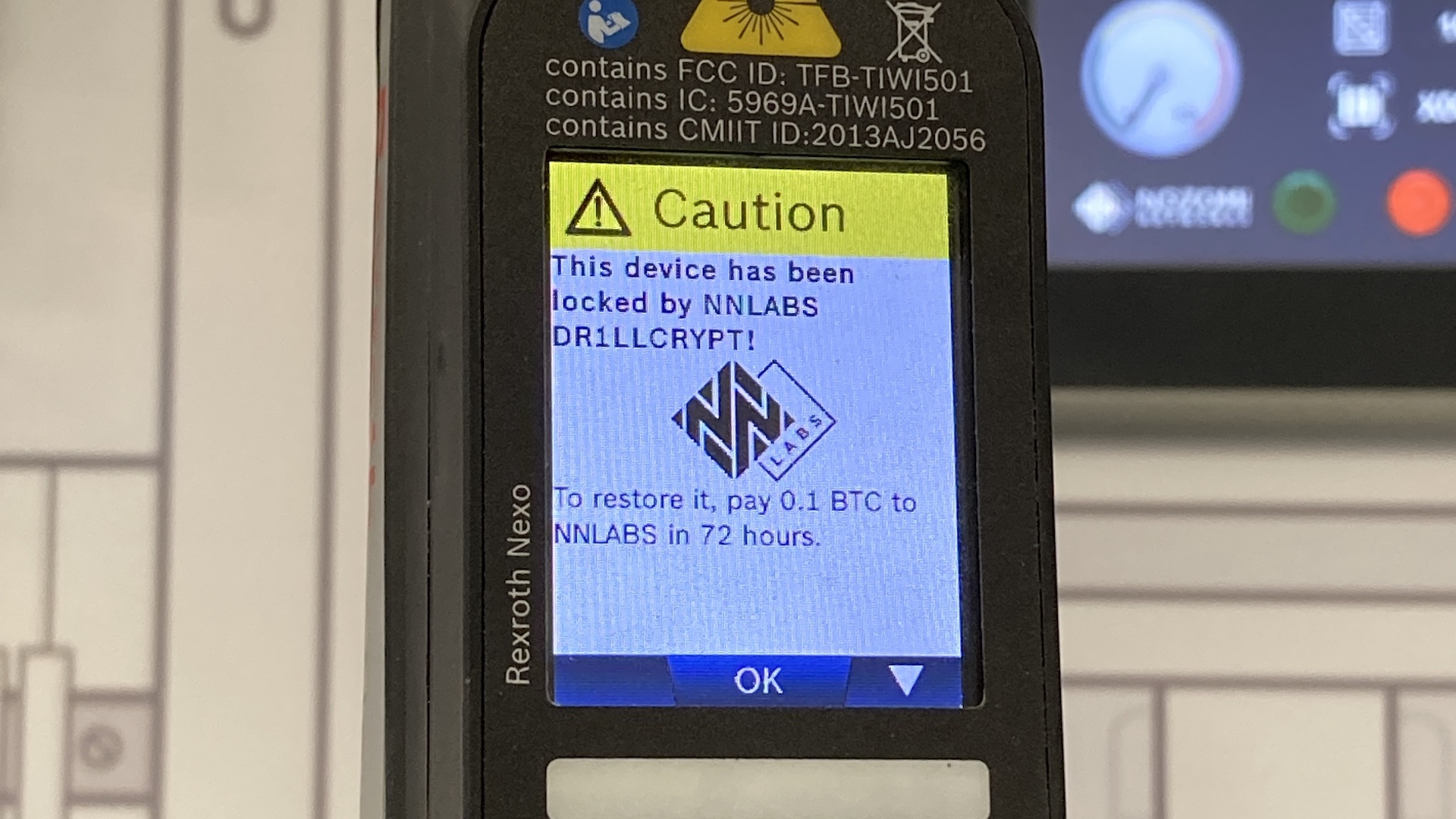
Nozomi says the software that does this is an “exposed management web application” with security problems. It’s possible for outside entities to send signals to the tool, or even install new code, changing the tool’s function or hijacking it entirely. In a test, Nozomi says it was able to use these to disable the tool and change the smart wrench’s screen to demand payment. In effect, Nozomi showed the tool is susceptible to ransomware attacks.
The group said automating such an attack would be easy, allowing a bad actor to take down an entire production line. Nozomi also posited a worse scenario, wherein an attacker could program the tool to deliver incorrect torque settings without telling the user, or logging the actual torque used. They could then inform the manufacturer of the flaw they introduced, and demand a ransom for information that could allow for a proper recall to be conducted.
Incorrect torque can cause anything from basic build quality problems to life-threatening hazards, such as in wheel lug nuts. (Ford recently had to recall trucks for inadequate lug nut torque.) Regardless of an automaker’s culpability or response, such a cyberattack could quickly turn into a scandal.

The Bosch tool in question will not remain vulnerable for long, as Bosch will reportedly roll out a security update this month to preclude such attacks. However, this security hole is representative of a broader problem across the “Internet of Things,” the subsurface deep web that’s used by all manner of services and technologies. Examples of devices that use these networks include security cameras and smart appliances, many of which are unsecured and at risk of similar, if less extreme forms of infiltration.
Got a tip or question for the author? You can reach them here: james@thedrive.com