Security in Information Technology means building firewalls to protect critical portions of the infrastructure. This added layer of protection helps prevent bad guys from accessing things that they’re not supposed to. Fast-forward to the mid-2010’s and we now find that automakers may soon have to do the same for their cars.
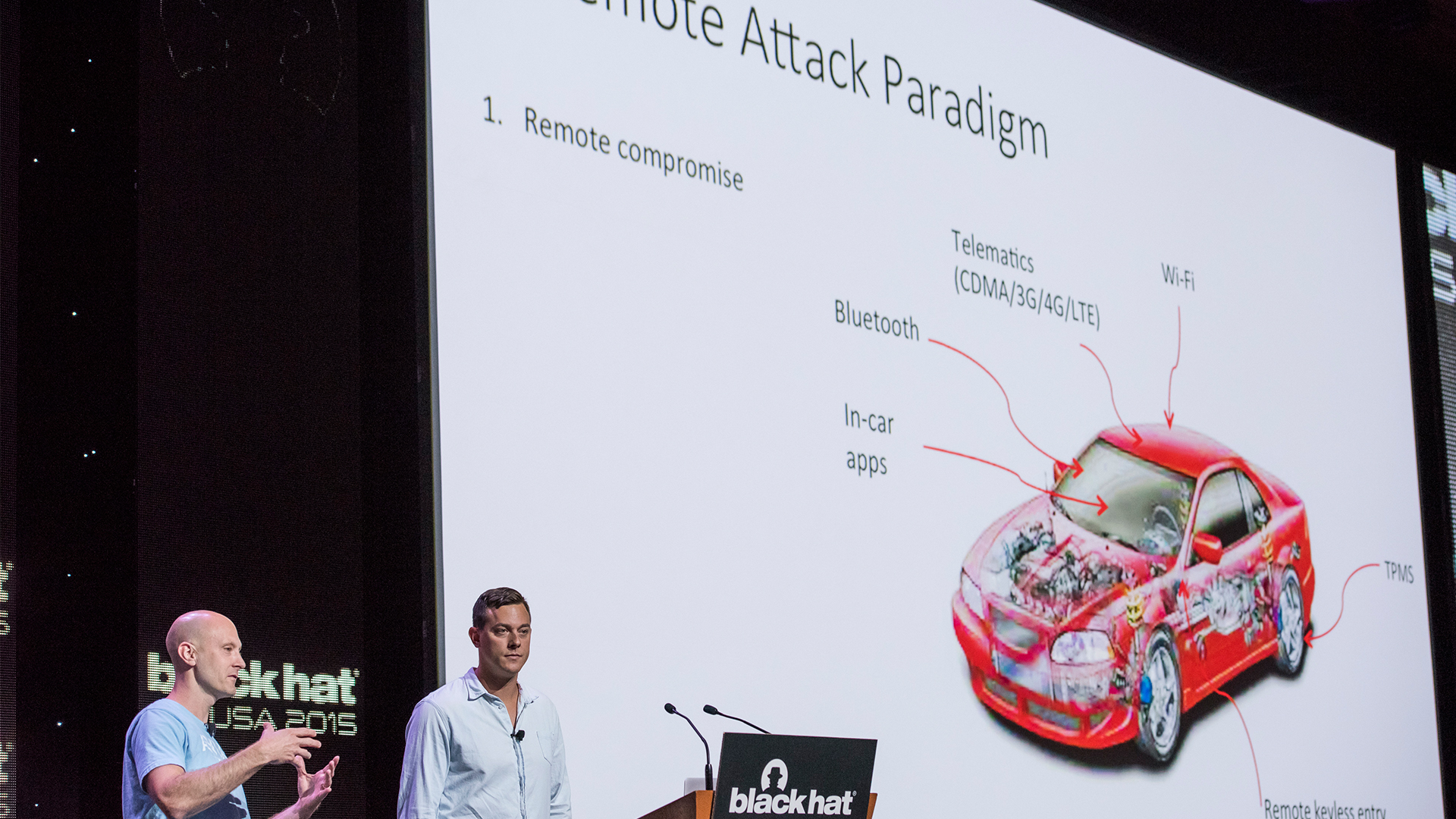
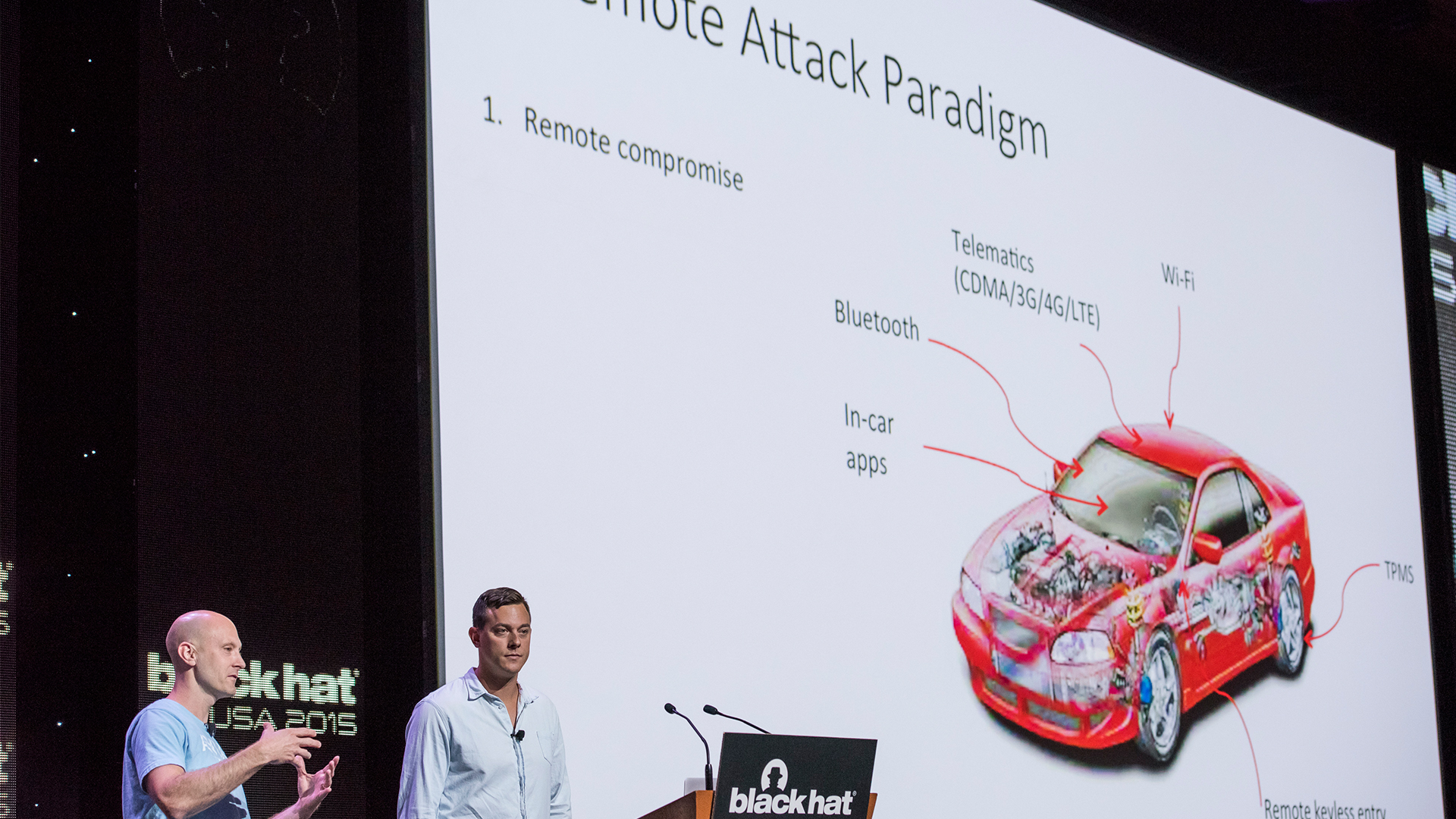
In 2015, Chrysler came under fire when several of its models were remotely accessed and taken control of after a report by Wired. Vulnerable vehicles all utilized Chrysler’s Uconnect platform, which operates by connecting to Sprint’s cellular network. Once the vehicle becomes internet facing, it is exposed to be accessible by attackers. In fact, the test performed did not even require knowing the unique IP Address of the vehicle. The attacker could scan the network, locate a Uconnect equipped vehicle, and start controlling it remotely.
“A set of GPS coordinates, along with a vehicle identification number, make, model, and IP address [were all accessible to the attacker]”
Wired
In a world becoming more connected every day, it becomes necessary to protect things which can be accessible by others. Two senators from Connecticut and Massachusetts have introduced a bill titled “Security and Privacy in Your Car (SPY Car) Act of 2017”. The bill, which names the NHTSA (National Highway Traffic Safety Administration) and FTC (Federal Trade Commission) as upholders of the law, seeks to prevent unauthorized users from accessing critical systems. These are defined as systems that if compromised could result in loss of controls of the vehicle. Essentially, this would equate to the Uconnect system being able to reach the internet, but if an attacker was to gain access and compromise your vehicle, they might be able to change your radio station, but couldn’t disable your brakes.
Additionally, a consumer-facing requirement was added to the bill which would require vehicle manufacturers to show what they have done to protect the driver from cyber attacks. This level of transparency extends to data collection, which must also be revealed to the driver who can opt-out of marketing which the manufacturer may sell.