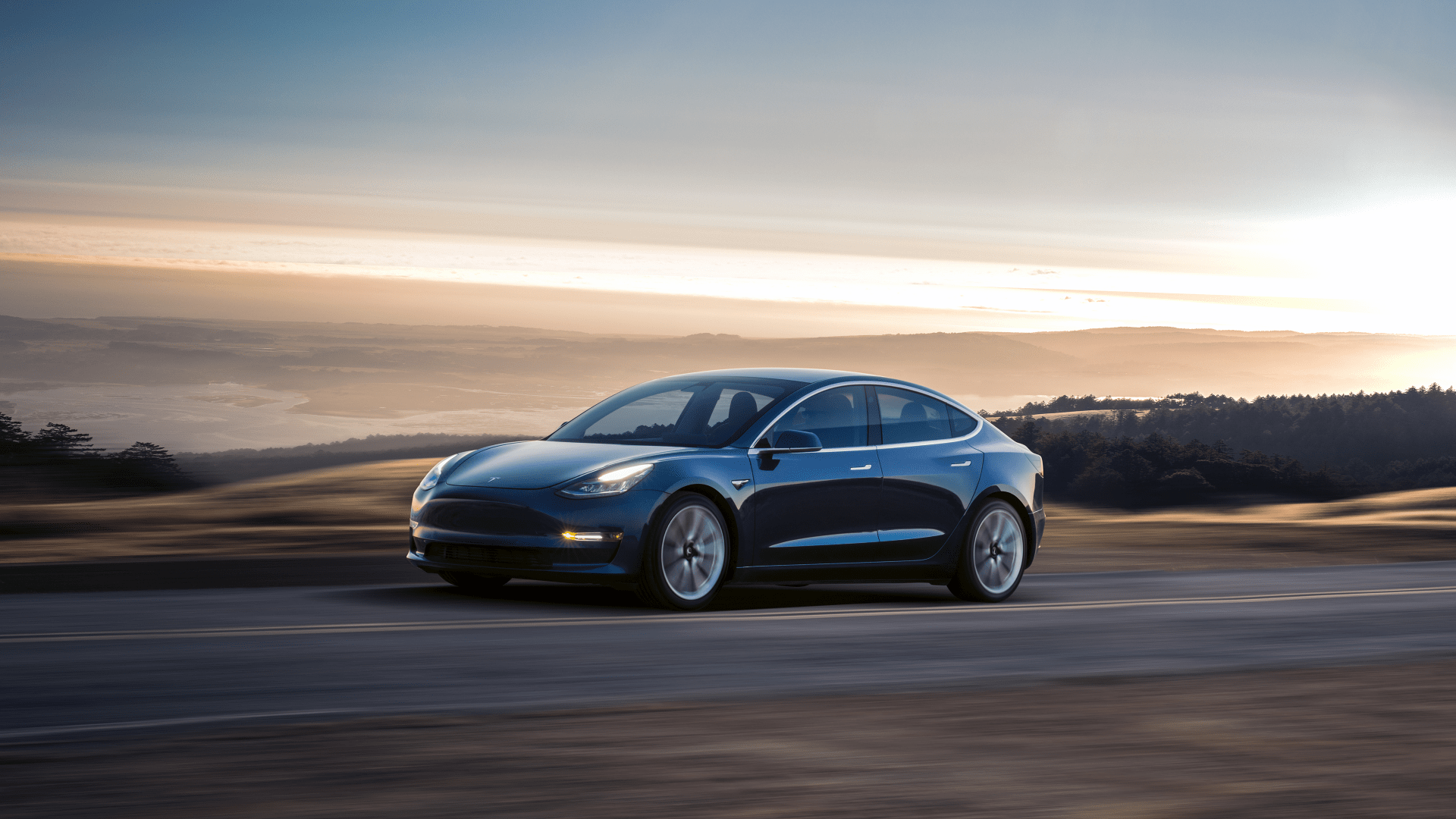
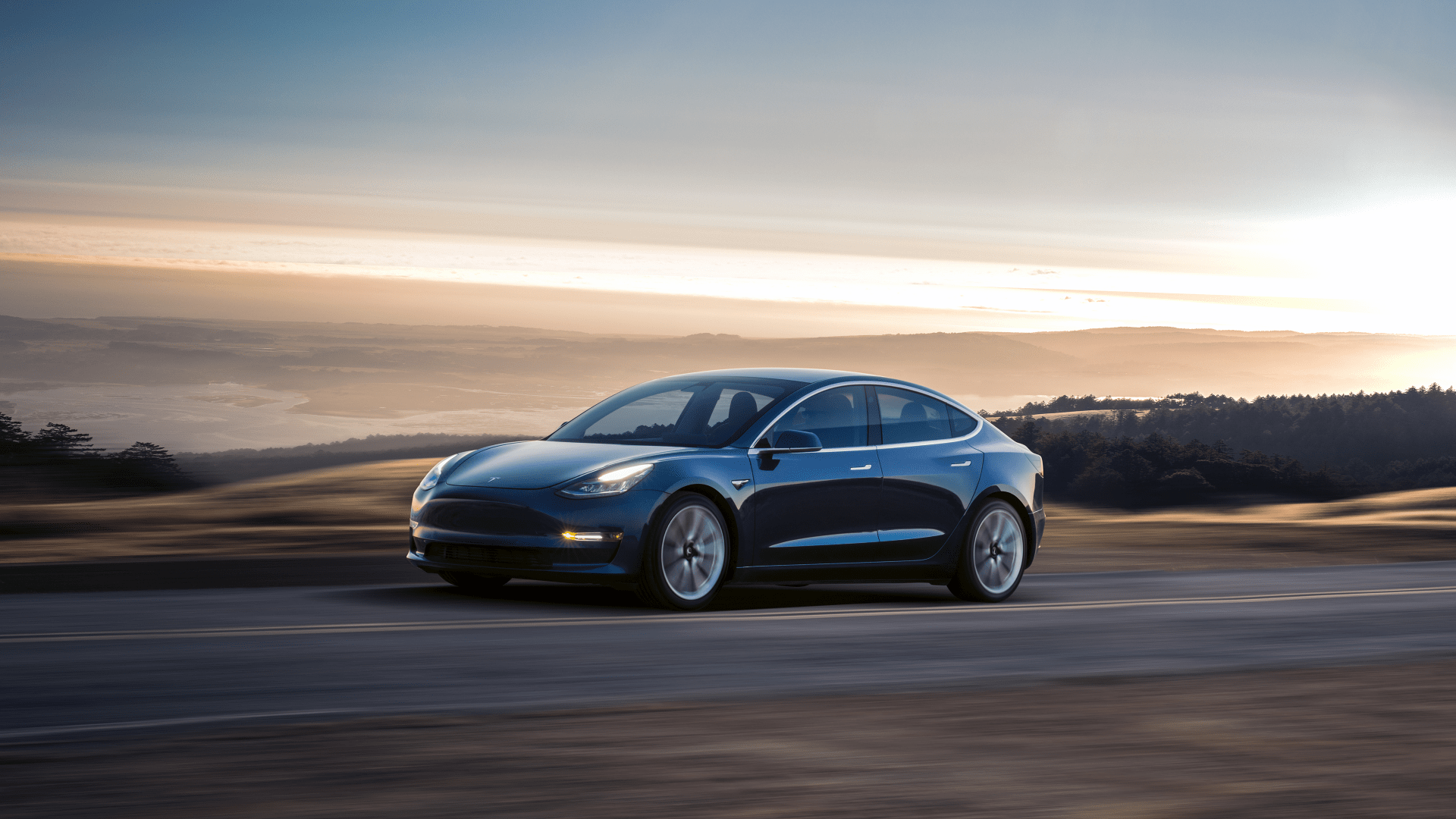
Twice each year at the CanSecWest’s Pwn2Own event in Vancouver, some of the world’s most determined white hat hackers step up to the plate in order to find exploits in certain products brought to the table. Toted as a zero-day initiative, the goal is to find holes previously unknown to the world and in return, the researchers responsible for finding the exploits are rewarded with some sort of prize (usually cold hard cash) called a bug bounty. This year, however, Pwn2Own will feature a new automotive category and give contestants the opportunity to drive away in a brand new Tesla Model 3 – but only if they can hack it.
Using a myriad of attack vectors, each contestant’s shared goal is to gain access to the Model 3 and its subsystems, or have it speak with a foreign actor other than Tesla. The first successful researcher to breach the Model 3’s security will drive away in a Tesla of their very own, but that’s on top of some already serious bug bounty cash. In fact, Tesla and other sponsors have ponied up a whopping $765,000 to spend on brilliant minds.
Here’s how each a successful hack in each category will pay out:
- Autopilot, Gateway, or VCSEC: $250,000
- Key Fob or Phone-as-Key: $100,000
- Modem or Tuner: $100,000
- Infotainment – Root/Kernel Exploit: $85,000
- Infotainment – Sandbox Escape: $85,000
- WiFi or Bluetooth: $60,000
- Autopilot – Denial of Service: $50,000
- Infotainment – Other: $35,000
Certain criteria must be met for the hack to be considered successful. For example, the contest does not deem relay or rolljam attacks as constituting a win related to the “Key Fob or Phone-as-Key” category. The infotainment hacks must be initiated by browsing to a particular web page using the vehicle’s in-car browser where code can be executed arbitrarily. And for each of the Gateway, Autopilot, or VCSEC”, “Model or Tuner”, or “WiFi or Bluetooth” categories, the attacker must execute code by redirecting communication to a rogue base station instead of its intended target.
One of the largest selling points of Tesla is its always-on approach to vehicle connectivity. Over-the-air updates with constant feature improvements make the car buying experience more of a service than a static product. Its location services, though sometimes been a topic of controversy for state-sponsored data farming, have made Tesla one of the most recovered theft vehicle brands in the United States. But all of that connectivity doesn’t come without risk; if data travels over the internet, someone somewhere could try to intercept it.
Tesla has mentioned that it has worked very hard to take a layered approach to the security fabric that controls the various functions in its vehicles. The electronics, powertrain, braking, and effectively every other large component on a Tesla has individualized encryption that, if breached, are seemingly walled-off from of other vehicle functions. That being said, in a world where everything is becoming increasingly connected, security should be one of the major focuses of every automaker who plans on delivering a connected experience to its customers.
The purpose of bug bounty programs like Pwn2Own is to find and patch exploits that could otherwise prove to be costly (or in the case of a connected car, deadly). With Tesla and other automakers rapidly accelerating to become the leader of new industry trends, security must be a focal point in order to retain customer safety and trust. And for one lucky white hat researcher, finding those bugs will land them in the driver’s seat.